tag
home / developersection / tag
How to improve the speed of website access and solve the problem of slow page loading
When developing a website, the website page loads much more importantly than other website server factors. The speed of website visits directly af
How Cyber Security Affects My Business: 10 Solutions
Due to millions of active domains, the ratio of cyber-attacks is also increasing day by day. The growing cyber incidents have made it compulsory for
Why Are VPNs The Best Solution To Stopping Cybercrime?
A virtual private network (VPN) is an encrypted tunnel that is used to create a secure connection between two computers. Now you can have a VPN wher
Protecting Your Business Against Ransomware Attacks
Ransomware attacks are on the rise. This will infect your computer’s files, locking them, then the cyberattacker demands a ransom to unlock the mali
What You Need to do to Keep Your E-commerce Website Safe
People can make money on the internet. There are plenty of ways to do this, but one of the best ways to build a lasting business on the internet is
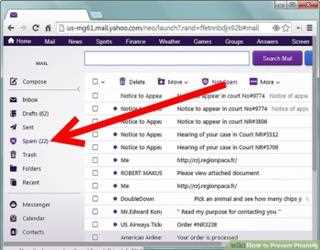
PHISHING ATTACK
What is phishing attack :Phishing is a type of social engineering attack through email, telephone, text massage for access all credentials, credit car
Is There A Privacy Threat for Big Data?
I was talking to a programmer friend the other day. He helps develop actuarial algorithms for insurance companies. He is constantly pointing out that his algorithms are beneficial to insurance companies and beneficiaries alike.
The reason: Why Individuals and corporations worry About Big Data
For the past several years, headlines have heralded the IoT as a game changer that will transform workplaces, optimize cities, and help individuals lead more efficient, healthier lives.
How Zero Knowledge Proof Will Enable Trustless Transactions and Increase our Privacy
While the challenges facing the future viability of Bitcoin and other cryptocurrencies remain unresolved, the underpinning technology that supports Bitcoin,
How to Inform Clients about the Realities of Cybersecurity
Cybersecurity is like the door ajar warning light on the console of a huge van going 80 mph down the freeway. Whoever’s driving the vehicle needs to pull over and close the door.
Ethical hacking- A license to hack
These days we are too much friendlier with the news of cybercrime in which the hackers perform activities which are illegal according to the laws. In
Cyber security
Cybersecurity refers to the security which includes the security and protection of computer systems from cyber-attacks, thefts, and damage to their hardware