You can envision a portion of the terrible assaults that anticipate an iOS gadget; this area talks about how the gadget is designed to withstand these sorts of assaults. Here we portray iOS 5, which as you'll see, is quite secure. In a later segment, we show you the development of how iOS arrived, which was somewhat of an uneven ride.
The Reduced Attack Surface
The assault surface is the code that procedures assailant provided input. If Apple has a powerlessness in some code, and either the assailant can't arrive at it or Apple doesn't send the code at all in iOS, an aggressor can't put together an endeavor concerning this defenselessness. Accordingly, a key practice is limiting the measure of code an aggressor can get to, particularly remotely.
Know more information about Latest iOS Development Trends
In the conceivable manners, Apple diminished the assault surface of iOS contrasted with Mac OS X (or different cell phones). For instance, love it or abhor it, Java and Flash are inaccessible on iOS. These two applications have a past filled with security vulnerabilities and excluding them makes it harder for an aggressor to discover an imperfection to use. In like manner, iOS won't process certain documents, however, Mac OS X will. One model is .psd documents. This record type is taken care of cheerfully in Safari, however not in MobileSafari, and significantly, no one would almost certainly see the absence of help for this dark document position. In like manner, one of Apple's organizations, .mov, is just mostly bolstered, and many .mov documents that play on Mac OS X won't play in iOS. At long last, even though iOS renders .pdf documents locally, just a few highlights of the record position are parsed. Just to see a few numbers regarding the matter, Charlie Miller once fluffed Preview (the local Mac OS X PDF watcher) and discovered well over a hundred accidents. At the point when he attempted these equivalent records against iOS, just 7 percent of them caused an issue in iOS. This implies just by diminishing the PDF highlights that iOS dealt with, it decreased the number of potential vulnerabilities by more than 90 percent for this situation. Fewer defects mean less open doors for misuse.
If you want to gain in-depth knowledge of the ios app development, you should enroll the free demo on iOS Online Training
The Stripped-Down iOS
Past simply lessening the potential code an assailant may misuse, Apple likewise stripped down the number of valuable applications an aggressor should use during and after abuse. The most evident model is that there is no shell (/canister/sh) on an iOS gadget. In Mac OS X abuses, the primary objective is to attempt to execute a shell in "shellcode." Because there is no shell at all in iOS, some opposite ultimate objectives must be produced for iOS misuses. In any case, regardless of whether there was a shell in iOS, it wouldn't be valuable because an assailant would not have the option to execute different utilities from a shell, for example, rm, ls, ps, etc. In this manner, aggressors who get code running should either play out the entirety of their activities inside the setting of the abused procedure or bring along every one of the devices they need to utilize. Neither of these alternatives is especially simple to pull off.
Privilege Separation
iOS isolates forms utilizing clients, gatherings, and other conventional UNIX record consent instruments. For instance, a considerable lot of the applications to which the client has direct access, for example, the internet browser, mail customer, or outsider applications, run as the client versatile. The most significant framework forms run as the special client root. Other framework forms run as different clients, for example, _wireless or _mdnsresponder. By utilizing this model, an aggressor who deals with a procedure, for example, an internet browser will be compelled by the reality the code she is executing will be running as a client portable. There are cutoff points to what such an adventure can do; for instance, the endeavor won't have the option to make framework level arrangement changes. In like manner, applications from the App Store are restricted in what they can do because they will be executed as clients versatile too.
Code Signing
One of the most significant security instruments in iOS is code marking. All parallels and libraries must be marked by a confided in power, (for example, Apple) before the bit will enable them to be executed. Moreover, just pages in memory that originate from marked sources will be executed. This implies applications can't change their conduct progressively or redesign themselves. Together, these activities keep clients from downloading and executing arbitrary records from the Internet. All applications must originate from the Apple App Store (except if the gadget is arranged to acknowledge different sources). Apple has a definitive endorsement and examines applications before they can be facilitated at the App Store. Along these lines, Apple assumes the job of an antivirus for iOS gadgets. It reviews each application and decides whether it is alright to run on iOS gadgets. This assurance makes it extremely difficult to get contaminated with malware. Just a couple of examples of malware have ever been found for iOS. The other effect of code marking is that it muddles misuse. When an endeavor is executing code in memory, it should download, introduce, and execute extra vindictive applications. This will be denied because anything it attempts to introduce won't be agreed upon. In this way, adventures will be limited to the procedure they initially misuse, except if it proceeds to assault different highlights of the gadget. This code marking insurance is the explanation individuals escape their telephones. Once jailbroken, unsigned applications can be executed on the gadget. Jailbreaking likewise kills different highlights (more on that later).
Data Execution Prevention
Typically, information execution anticipation (DEP) is a system through which a processor can recognize which bits of memory are executable code and which segments are information; DEP won't permit the execution of information, just code. This is significant because when an adventure is attempting to run a payload, it might want to infuse the payload into the procedure and execute it. DEP makes this unimaginable because the payload is perceived as information and not code. How aggressors ordinarily attempt to sidestep DEP is to utilize return-situated programming (ROP), which is examined in Chapter 8. ROP is a system wherein the aggressor reuses existing legitimate code bits, commonly in a way never planned by the procedure, to complete the ideal activities. The code-marking component in iOS acts like DEP yet is significantly more grounded. Run of the mill assaults against DEP-empowered frameworks use ROP quickly to make an area of memory that is writable and executable (and subsequently where DEP isn't authorized). At that point, they can compose their payload there and execute it. In any case, code marking necessitates that no page might be executed except if it begins from code marked by a confided in power. Along these lines, when performing ROP in iOS, it is beyond the realm of imagination to expect to kill DEP like an assailant regularly would. Joined with the way that the adventure can't execute applications that they may have written to circle, this implies abuses should just perform ROP. They may not execute some other sorts of payloads, for example, shellcode or different doubles. Composing huge payloads in ROP is very tedious and complex. This makes the misuse of iOS more troublesome than pretty much some other stage.
Address Space Layout Randomization
As talked about in the past area, how assailants attempt to sidestep DEP is to reuse existing code pieces (ROP). Be that as it may, to do this, they have to know where the code sections they need to reuse are found. Address space format randomization (ASLR) makes this troublesome by randomizing the area of articles in memory. In iOS, the area of the double, libraries, dynamic linker, stack, and pile memory addresses are altogether randomized. At the point when frameworks have both DEP and ASLR, there is no nonexclusive method to compose an endeavor for it. By and by, this generally implies an aggressor needs two vulnerabilities — one to get code execution and one to release a memory address to perform ROP — or the assailant might have the option to get by with having just a single exceptionally unique weakness.
Sandboxing
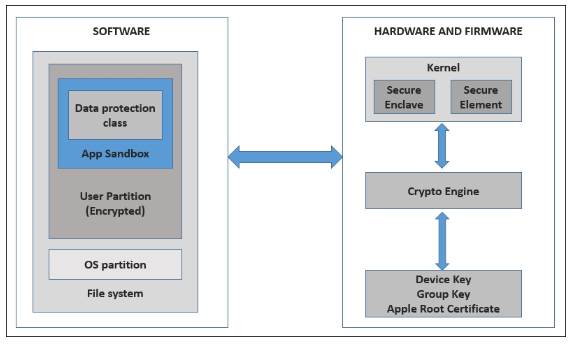
The last bit of the iOS resistance is sandboxing. Sandboxing permits significantly better-grained power over the activities that procedures can perform than the UNIX authorization framework referenced before. For instance, both the SMS application and the internet browser run as client versatile, however, perform altogether different activities. The SMS application most likely needn't bother with access to your internet browser treats and the internet browser needn't bother with access to your instant messages. Outsider applications from the App Store shouldn't approach both of these things. Sandboxing takes care of this issue by enabling Apple to determine precisely what consents are fundamental for applications. (See Chapter 5 for more subtleties.) Sandboxing has two impacts. In the first place, it confines the harm malware can do to the gadget. If you envision a bit of malware having the option to overcome the App Store survey process and being downloaded and executed on a gadget, the application will, in any case, be constrained by the sandbox rules. It might have the option to take all your photographs and your location book, however, it won't have the option to send instant messages or make telephone calls, which may straightforwardly cost you cash. Sandboxing additionally makes misuse more enthusiastically. If an aggressor finds a powerlessness in the diminished assault surface, figures out how to get code executing regardless of the ASLR and DEP, and composes a gainful payload altogether in ROP, the payload will at present be restricted to what is available inside the sandbox. Together, these assurances make malware and abuse troublesome, although certainly feasible.


Leave a Comment